Security is an essential component of any application that includes critical functionality. This can be as simple as protecting your database from malicious actors as it can be as complex as applying fraud detection to a qualified lead before importing them into your platform.
Security applies to all phases of the software development life cycle (SDLC) and should be at the forefront of your developers’ minds as they implement the requirements of your software. In this article, we’ll look at how to create a secure SDLC, which will help you catch issues in requirements before they become security issues in production.
Security issues can be addressed in the SDLC pipeline well before deployment to production with dedicated effort. This reduces the likelihood of discovering security vulnerabilities in your app and works to mitigate the impact if they are discovered.
The goal of Secure SDLC is not to completely eliminate traditional security checks, such as penetration tests, but rather to incorporate security into developer responsibilities and empower them to build secure applications from the start.
Why Is Secure SDLC Necessary?
Because application security is critical, secure SDLC is essential. The days of releasing a product and then fixing bugs in subsequent patches are over. Developers must now be aware of potential security issues at every stage of the development process. This necessitates incorporating security into your SDLC in ways that were not previously necessary. Because anyone can potentially gain access to your source code, you must code with potential vulnerabilities in mind. As a result, having a strong and secure SDLC process is critical to ensuring that your application is not vulnerable to attacks from hackers and other malicious users. New tools, such as application security posture management, can aid in providing a comprehensive picture.of the components of your application security setup, as well as provide context about vulnerabilities.
In the next section, we will explore the specific ways in which O2 technologies, in conjunction with AI, are revolutionizing the manufacturing landscape and furthering the goals of Industry 4.0.
An Overview of SDLC Practises
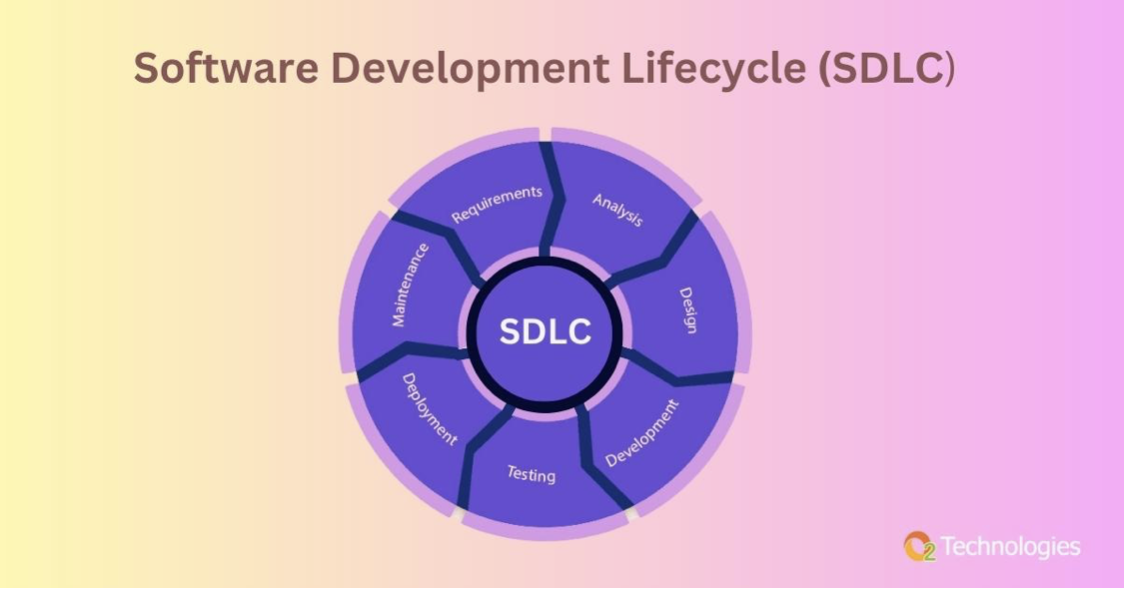
The Software Development Lifecycle (SDLC) describes the process of creating software applications. It usually includes the following stages:
- Gathering of requirements
- Requirements analysis to guide design
- Creating new features based on requirements
- Creating new capabilities (writing code to meet specifications)
- Testing and verification of new capabilities to ensure that they meet the requirements
- Launch of the new project
- After the release, these capabilities must be maintained and evolved.
The Waterfall model is one of the earliest and most well-known SDLC methodologies, and it served as the foundation for these SDLC phases. These phases, which were developed in 1970, largely remain the same today, but there have been enormous changes in software engineering practises that have redefined how software is created.
Software was traditionally written for highly specialised applications, and software programmes developed using the Waterfall methodology often took years to release. Modern practises now prioritise increasing the rate of innovation while maintaining the quality of software applications. Companies have moved away from Waterfall, with the majority employing some form of the agile SDLC, which was first published in 2001.
Agile development advocates breaking up large monolithic releases into multiple mini-releases, each completed in two or three-week sprints, and employs automation to build and test applications. This enables businesses to iterate much more quickly. Rather than the infrequent, monolithic deployments typical of Waterfall-driven applications, agile development frequently focuses on releasing new functionality multiple times per day, building software incrementally rather than all at once.
Application Security and SDLC
But what about the applications’ security? Most attacks in 1970 required physical access to a terminal on the machine running the application. The world was also much less interconnected, which reduced the risk of external actors interfering with application security. Security was compromised as new software development methodologies were implemented over time.
Instead, application security fell under the purview of IT security teams devoted to application support. Initially, applications were only tested after they were released. This testing took place in production environments, frequently on a yearly basis. Unfortunately, this meant that any potential vulnerabilities would be “out in the wild” for attackers to exploit for weeks, if not months, before they were discovered and fixed. As a result, most businesses now supplement production testing with pre-release security testing. This supplemental testing was added to the release’s critical path, and applications had to pass the security check before deploying the code to production.
This security testing step frequently takes several weeks, lengthening the release cycle. Worse yet, its outcome is completely unpredictable: A security test may uncover only a few vulnerabilities that can be addressed in a few days, or it may uncover dozens or even hundreds of vulnerabilities. Fixing the discovered vulnerabilities may necessitate significant code changes that replace entire underlying components, all of which must then be validated against both the application requirements and another security test.
This can, and frequently does, set back application developers by weeks as they try to meet now-impossible release deadlines. This causes a lot of friction within organisations and forces them to choose between two bad options: “signing off” on risk and releasing an application with vulnerabilities or missing delivery targets (or both). Worse, fixing an issue discovered this late in the SDLC can cost up to 100 times more than simply fixing it earlier in the process (more on this later).
As the rate of innovation and the frequency of software releases has increased over time, all of these issues have gotten worse. As a result, the role of application security in the software development process has been reimagined, and a secure SDLC has been created.
What are the processes of the Secure Software Development Life Cycle?
SDLC security impacts every stage of the software development process. It necessitates a mindset that is focused on secure delivery, raising issues as they are discovered during the requirements and development phases. This is far more efficient—and far less expensive—than waiting for these security flaws to manifest in the deployed application. Secure software development life cycle processes include security at every stage of the SDLC.
While incorporating security into every phase of the SDLC is, first and foremost, a mindset that everyone must adopt, security considerations and associated tasks will differ significantly by SDLC phase.
The Secure Software Development Life Cycle has five stages.
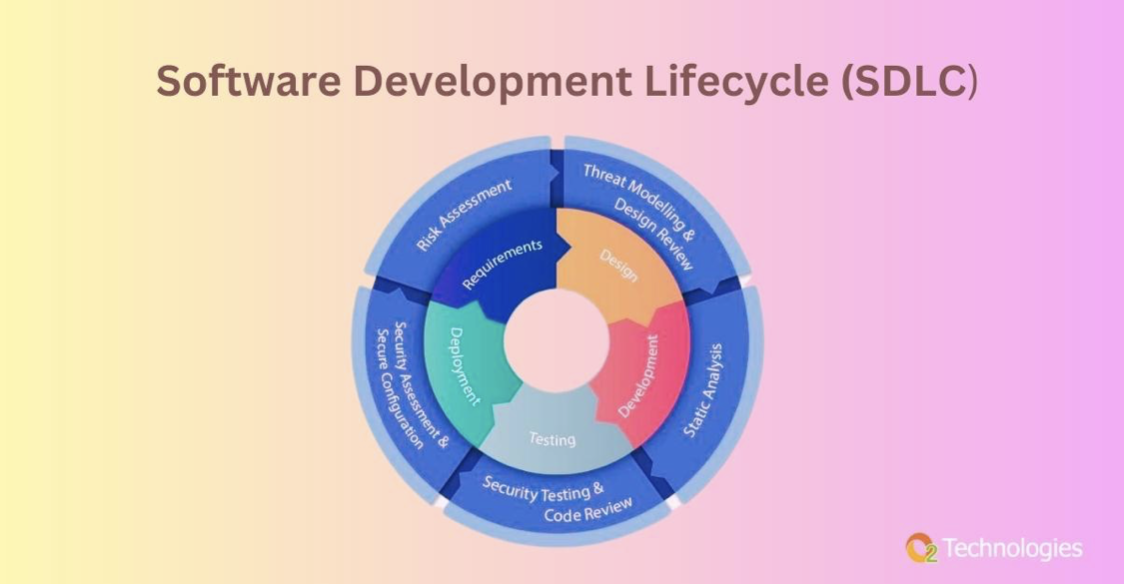
Each phase of the SDLC must contribute to the overall application’s security. This is done differently for each phase of the SDLC, with one important note: Software development life cycle security must be at the forefront of everyone’s minds. Consider the following secure software development life cycle scenario for a team developing a membership renewal portal:
Phase 1: Prerequisites
During this preliminary stage, requirements for new features are gathered from various stakeholders. It is critical to identify any security concerns when gathering functional requirements for the new release.
- Example functional requirement: Before renewing their membership, the user must be able to verify their contact information.
- As an example of security, users should be able to see only their own contact information and not anyone else’s.
Phase 2: Design
This phase translates in-scope requirements into a plan for how the actual application should look. In this context, functional requirements typically describe what should happen, whereas security requirements typically focus on what should not happen.
- Example functional design: the page should retrieve the user’s name, email, phone number, and address from the database’s CUSTOMER_INFO table and display it on screen.
- Before retrieving information from the database, we must verify that the user has a valid session token. If this is not the case, the user should be redirected to the login page.
Phase 3: Development
When it comes time to actually implement the design and make it a reality, the focus usually shifts to ensuring that the code is well-written from a security standpoint. Secure coding guidelines are usually established, as are code reviews to ensure that these guidelines are followed correctly. These code reviews can be done manually or automatically using technologies like static application security testing (SAST).
However, because the vast majority of modern applications aren’t written from scratch, modern application developers can’t be solely concerned with the code they write. Developers instead rely on existing functionality, which is typically provided by free open source components, to deliver new features and thus value to the organisation as quickly as possible. In fact, these open-source components are used in 90% or more of modern deployed applications. Typically, open-source components are tested using Software Composition Analysis (SCA) tools.
In this case, secure coding guidelines may include:
- Using parameterized, read-only SQL queries to read data from the database and minimising the possibility that these queries can ever be hijacked for malicious purposes.
- Validating user inputs before processing the data they contain
- Sanitising any data that is returned to the user from the database.
- Before using open source libraries, check for vulnerabilities.
Phase 4: Validation
During the Verification phase, applications are thoroughly tested to ensure they meet the original design and requirements. This is also an excellent opportunity to introduce automated security testing utilising various technologies. Unless and until these tests pass, the application will not be deployed. To control verification and release, this phase frequently includes automated tools such as CI/CD pipelines.
- At this stage, verification may include:
- Automated tests that express your application’s critical paths
- Automated execution of application unit tests that validate the underlying application’s correctness.
- Tools for automating deployment that dynamically swap in application secrets for use in a production environment.
Phase 5: Upkeep and Evolution
The story does not end with the release of the application. In fact, vulnerabilities that slipped through the cracks in the application may be discovered long after it has been released. These flaws may exist in the code that developers wrote, but they are increasingly being discovered in the underlying open-source components that comprise an application. As a result, the number of “zero-days”—previously unknown vulnerabilities discovered in production by the application’s maintainers—increases.
The development team must then patch these vulnerabilities, which may necessitate significant rewrites of application functionality in some cases. Vulnerabilities at this stage may also come from other sources, such as external penetration tests performed by ethical hackers or public submissions through “bug bounty” programmes. These types of production issues must be anticipated and accommodated in future releases.
The Advantages of SSDLC
Secure SDLC is the epitome of a “shift-left” initiative, which refers to incorporating security checks as early in the SDLC as possible.
This allows development teams to properly plan releases, making it easier to detect and address issues that may affect the release timeline. This is far preferable to an unpleasant surprise when the application is deployed to production. As a result, SSDLC aids in keeping releases on track.
Furthermore, at its core, SSDLC’s security efforts are led by the development team itself. This allows the domain experts who wrote the software to fix the issues rather than having a different team fix the bugs as an afterthought. This enables developers to take responsibility for the overall quality of their applications, resulting in more secure applications being deployed in production.
While the extra effort of security testing within the SDLC process may appear to be a lot of work and an expensive investment, the vast majority of it is now automated. This is especially true for development operations, also known as DevOps (more on this later). The secure SDLC environment necessitates frequent collaboration between DevOps and the engineers implementing the application’s functionality, which must be built into the SDLC itself.
Development teams can reduce the total cost of ownership of their applications by addressing these issues early in the process. As shown in the chart below, discovering issues late in the SDLC can result in a 100-fold increase in the development cost required to fix those issues.
Transitioning to secure SDLC, as shown in Figure 2, enables development teams to build secure applications more quickly, and may thus be a worthwhile investment for organisations.

How Can SSDLC Be Assured?
A secure SDLC necessitates a focus on both how the application works and how developers translate requirements into application code. As the application is being developed, security must be at the forefront of the team’s mind. This may necessitate a cultural shift within your teams, as well as the implementation of automated processes and checks at each stage of software development.
Ensuring SSDLC for an application is highly dependent on the strengths and weaknesses of the software development team working on SDLC security, making it difficult to pinpoint a solution.
Because secure SDLC entails changing existing processes, implementing new tools, and, more importantly, driving a cultural change across multiple teams, the path to well-functioning secure SDLC is usually unique to each organisation and can even differ across business units.
Best Practises for Secure SDLC
1. Inform Your Developers
- 1. Secure SDLC works in tandem with a number of related initiatives, including:
- 2. Developing guidelines for secure coding
- 3. Security awareness and secure coding training for developers
- 4. Setting clear expectations for how quickly production issues must be addressed (also known as remediation SLAs).
- 5. Not all of these things must occur for an effective SSDLC implementation, but, like a jigsaw puzzle, you must put enough pieces together before you can see the big picture.
2. Have Specific Requirements
Whatever you create should be simple to grasp. Development teams require clear requirements that are simple to implement. This applies to all security recommendations, guidelines, and advice. Any flaws discovered during testing must be easy to exploit. It is critical that all people, processes, and tools involved bring solutions to the table rather than simply pointing out problems.
3. Keep a Growth Mindset
Because SSDLC will alter the way multiple teams work and interact, it is critical that everyone enters this experience with an open mind, and that the security team has the mindset of empowering developers to secure their own applications.
4. Connect Initiative Implementation to Other Initiatives
SSDLC changes may be easier to implement for well-established applications and teams when they are linked to another modernization effort, such as a cloud transformation, a DevOps initiative, or its more security-conscious variant, DevSecOps.
5. Address the Major Issues First
Rather than addressing every vulnerability discovered, concentrate on the most critical issues and actionable fixes. While it may be possible for newer or smaller applications to address every security issue, this will not always be the case for older or larger applications. A triage strategy can also be beneficial. This focuses not only on preventing security issues from entering production, but also on triaging and addressing existing vulnerabilities over time.
Check out our full list of SDLC best practises for more best practise tips on securing your SDLC
DevSecOps and SSDLC
The relationship between SSDLC and DevSecOps must be discussed. They are occasionally used interchangeably, which can cause confusion. While SSDLC and DevSecOps are closely related, the two practises are actually complementary. SSDLC and DevSecOps both aim to give developers more ownership over their applications, ensuring that they are doing more than just writing and testing code to meet functional specifications.
Secure SDLC focuses on how the application is designed and built; DevSecOps aims to shift ownership of each application’s production environment away from traditional IT teams and into the hands of the developers. This allows developers to focus on automating as many build, test, and release processes as possible.
DevOps and DevSecOps have started a revolution in redefining software developers’ roles. This has been aided by other significant changes, such as cloud transformations. While empowering developers and speeding up security testing is critical to most modern organisations’ success, it would be a mistake to view application security as merely an automation challenge. Rather, it is critical to drive cultural and process changes that promote security awareness and considerations early in the development process. This must permeate all aspects of the software development life cycle, whether it is referred to as SSDLC or DevSecOps.
Towards a More Secure Future
Traditional methods of testing for vulnerabilities in production are no longer adequate for protecting your applications. As the software industry has evolved, so have the types of attacks. To deploy and maintain a secure application, every step of the application development process must be secured. This includes asking questions about security behaviours during the requirement gathering stage, modifying team culture and practises to account for a security-oriented mindset, incorporating automated verification into you deploy process, and a variety of other practises that contribute to a secure SDLC process.
Instead of having to backtrack from the maintenance phase, SSDLC allows you to shift security risks to the left, addressing the source of security issues at the requirements phase. You can be confident that your application will be far more secure as a result of focusing on security at every stage of development.
O2 Technologies’ tooling offers integrated, automated security to meet your governance and compliance requirements.
